"Misty" storage can be a safe alternative to cloud-based
 Source:
Source:
Working in the field of computer technologies Italian scientists create a new concept of remote distributed storage of documents, where the benefits of cloud computing would remain the same, but without the attendant security flaws cloud computing, which are generated by the fact that the documents are stored entirely on a single remote server. Instead, scientists have proposed the technique in which files do not have specific places where they would permanently reside. The data packets are in motion on the network.
Culmone Rosario (Rosario Culmone) and Maria Concetta De vivo (De Vivo Maria Concetta) from the University of Camerino noted that cloud computing contain certain aspects of risk. These aspects arise from the essence of technology. Another approach may consist in the fact that the files will have a certain storage on the server. The development team is following the "cloud" traditions, also picked up their technology, "weather" metaphor, calling it "vague". The results of the study were published by scientists in the publication of the International Journal of Electronic Security and Digital Forensics.
Metaphor accurately captures the essence of the new development. After all, fog, unlike clouds, scattered in the air and finds sustainable forms, constantly before our eyes, changing their bizarre shapes. Continuous dynamics — it provides a semblance of a new approach to remote computer storage irregular natural phenomenon, which gave it its name.
As an alternative to cloud storage, the obscure store not assume file storage on a single server. Thus, it is rather the fog of files than a dense cloud. A specific location where files would be placed entirely within the new technology simply does not exist.
The New concept involves the distribution of files over public or private networks, without fixed storage locations. Thus, there is no single server which you can use to access these files. They will be available to only those users who have that right.
The New technology uses standard network protocols, but in an unusual way. Through the "virtual" buffers of Internet routers it provides endless movement of data packets and, thus, the file will not reside on the same computer.
materials sciencedaily.com
Recommended
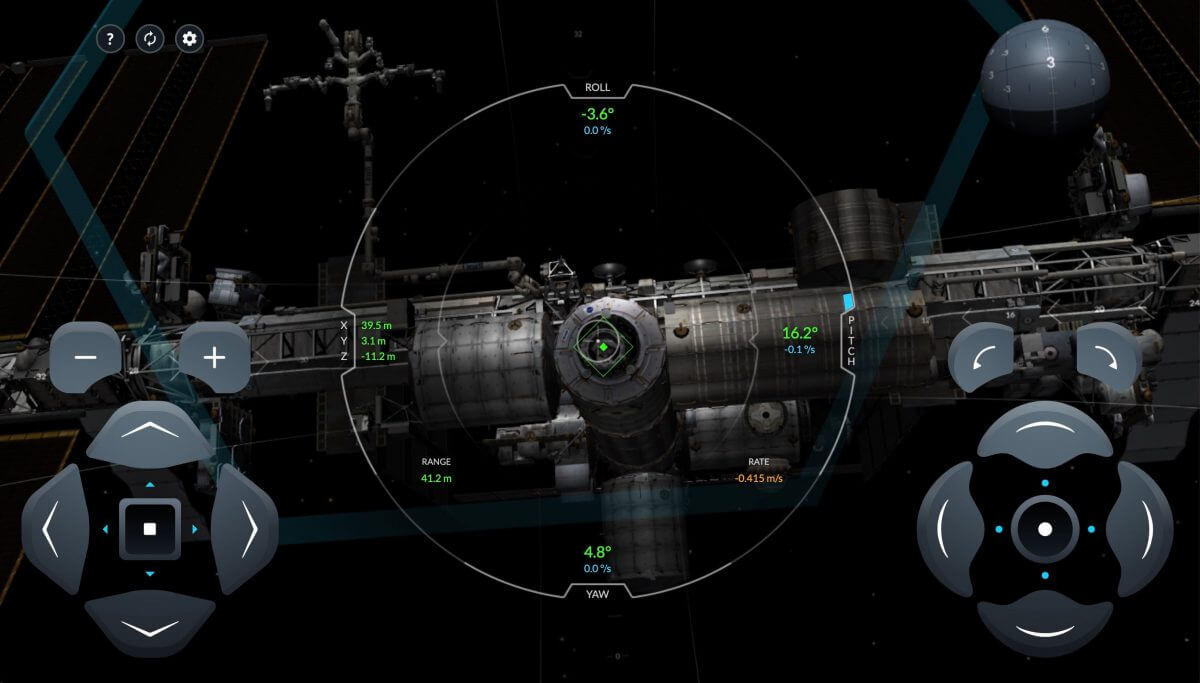
And you can? SpaceX has released a real simulation of Crew Dragon docks with ISS
this month a new spacecraft from SpaceX Crew Dragon will deliver its first passengers to the International space station. How will this happen? Now you can see what the astronauts see when approaching the ISS. SpaceX has released the real online simu...
What the company will definitely survive the pandemic?
In the world in the midst of a pandemic coronavirus, which has already affected millions of people. And I'm not talking only about those who were infected, but also about those who have lost a job, got laid wages or even can no longer conduct busines...
Will we be able to survive without the Internet?
do you think we are still the ones who roamed the earth thousands of years, or we become a new society — society ONLINE? Almost like in the cult movie the Matrix. I have long thought that we are very dependent on the Internet, but wonder how. L...
Related News
Google has figured out how to make reCAPTCHA invisible
to Be a robot in our days is becoming increasingly difficult. The ingenious developers of websites and web services to create more sophisticated checks on the activities of bots in the Network. If before we were forced to introduc...
Qutee.com — artificial intelligence in the service of marketing
In the era of "posttrade" it is believed that what we love, what they believe and what they want — all this is imposed on us from outside. PR people, marketers, spin doctors, advertisers — all of these people relentles...
AI from Facebook will determine suicidal users
according to the BBC news service, social network Facebook has developed algorithms for artificial intelligence are capable of, based on specific behavioral reactions and communication styles of people, find the users who are in v...
Social networks and messengers in a single app? No longer a dream
not long ago it was fashionable to have dozens of different applications that essentially could be combined into one, now the trend is back — instead of separation it's aggregation. This time to combine will be the most impo...
Wikipedia broke real hidden cyber war between the bots
Wikipedia is one of the most popular websites on the Internet (according to itself, Wikipedia, reference data Alexa Internet and SimilarWeb). On the running in 2001, the website to date contains more than 40 million articles on va...
Everyone loves to do a selfie, but to look at other people's selfies – no
the So-called selfie (the term was even added to the Oxford English dictionary), which are surrounded by modern social networks represent the imprinting itself on the camera. This cultural phenomenon is now so widespread that the ...
A slight miscalculation: a service to store code Networks accidentally deleted almost all the data
Yesterday evening, January 31, a service to store code Networks were unavailable. It turns out that the system administrator accidentally… deleted almost everything. Made mistakes at different stages of copying databases fro...

























Comments (0)
This article has no comment, be the first!