Tag Hacking - results: 13
Hackers can kill people with pacemakers, but there are
We already know how hackers can harm computers, smartphones and other technology. Few people is aware that under the threat of hacking and there are other devices that are directly connected to health and even life of people. Thes...
The scooters Xiaomi found a vulnerability that allows anyone to control them remotely
electric vehicles — well, and even better when you can take it with you — for example, the scooter. But the more complex the technology, the more it appears vulnerabilities. Thus, the American company Zimperium which s...
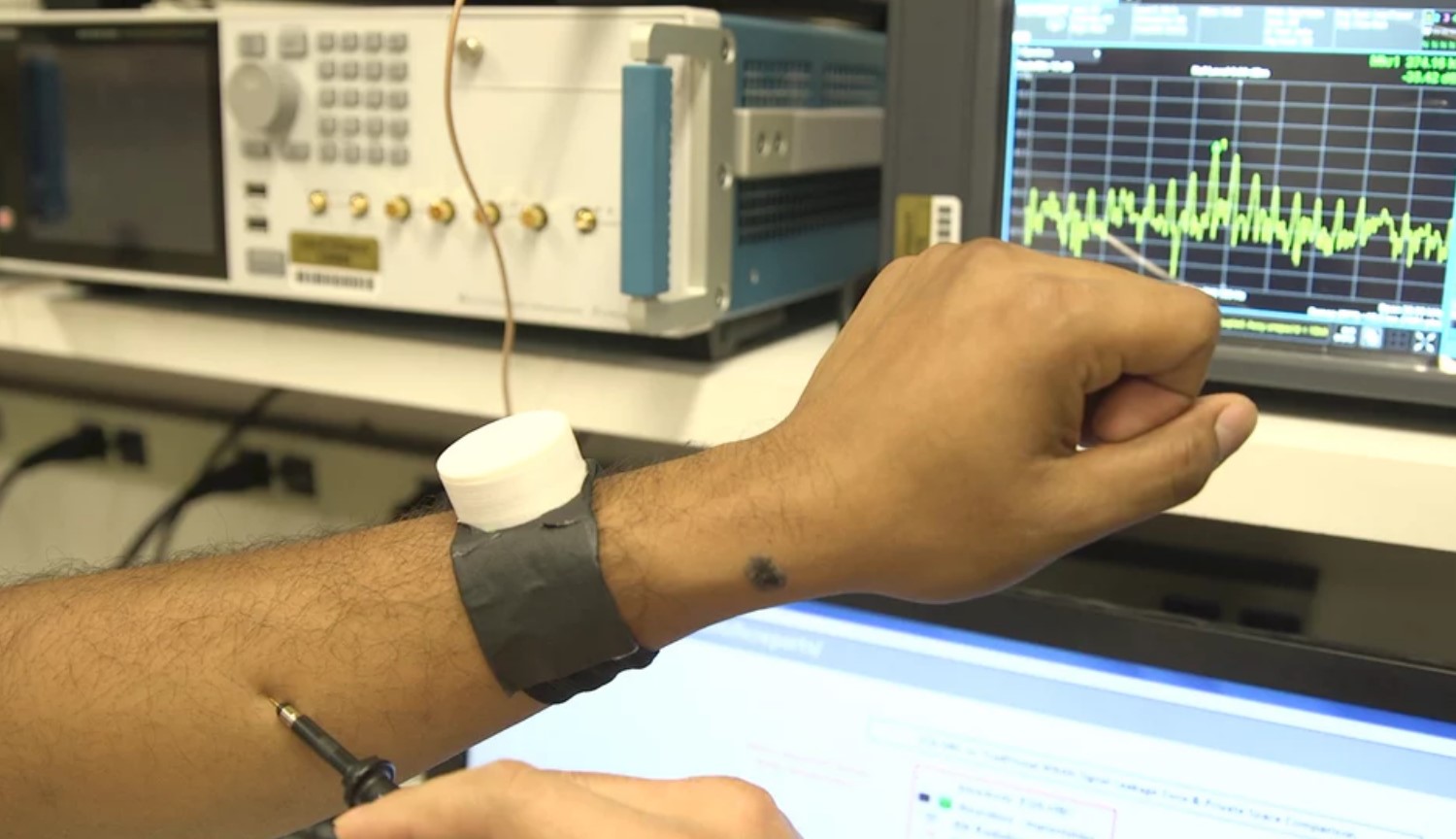
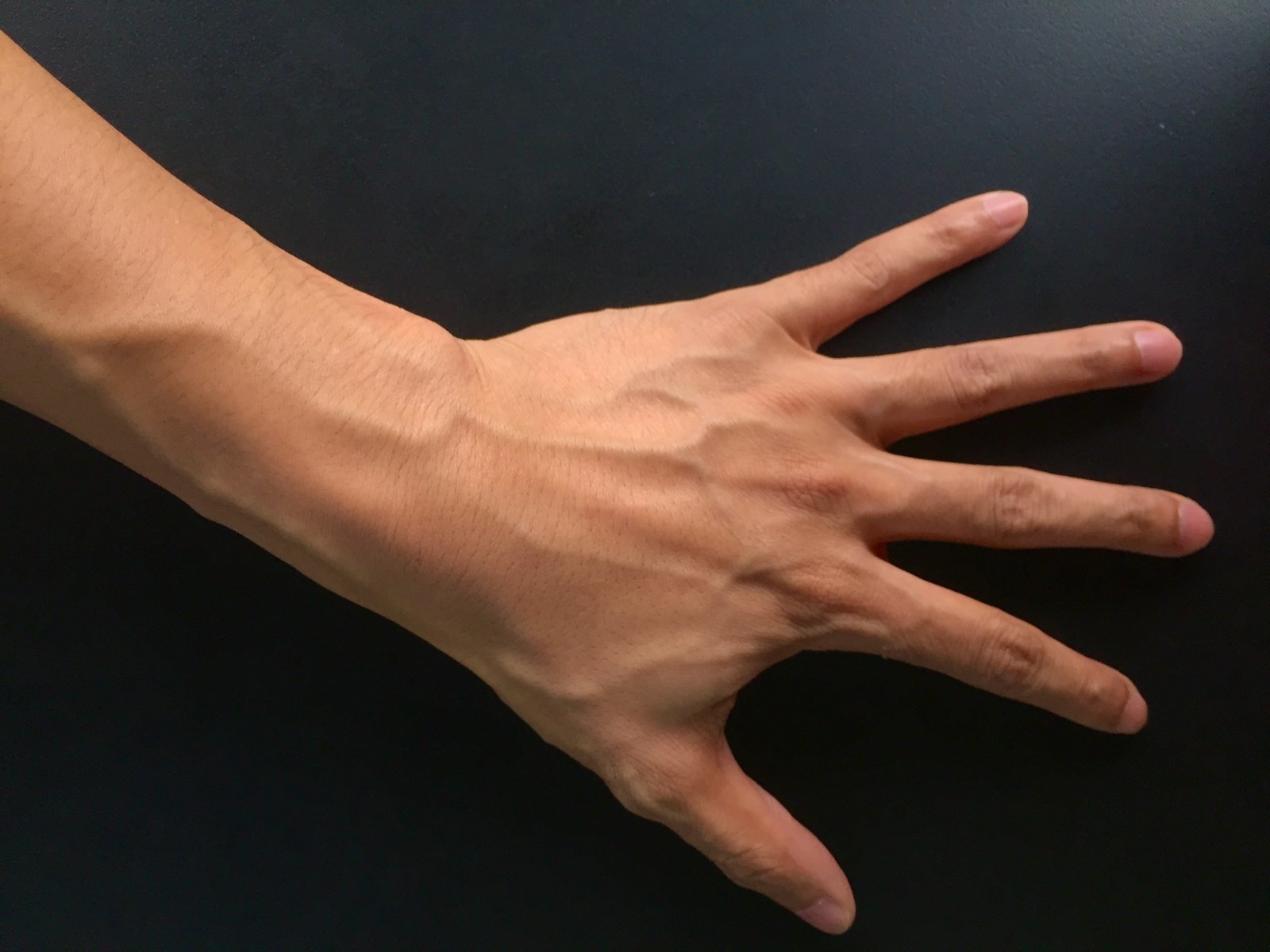
Hackers have bypassed one of the most complex security systems
Experts in the field of computer security, spoke about how hackers can easily circumvent the authorization system based on scanning and analysis of the subcutaneous blood vessels. How this is done, the researchers of biometric aut...
Hack the phone using speaker and microphone? Easy!
Modern smartphones offer the user a lot of opportunities, but also expose personal data like passwords and credit card numbers at risk of being stolen. Of course, there are many options to protect your device from antivirus progra...
Users of computers began to threaten the publication of personal videos and browser history
computer Users around the world have started to receive e-mails from Scam to extort money. Depending on who sent the letter, its contents may change. However, colleagues from Business Insider was able to extract common features in...
The hacker stole the files of the U.S. army, but could not sell them even for $ 150
the Hacker has guessed to use the vulnerability of routers to gain access to the files of the U.S. army. The obtained data he attempted to sell on the forum on the darknet, but was unable to find an interested buyer, even reducing...
The hacker group seized control of satellites and operators
Researchers in the security area of Symantec Corp. discovered a sophisticated hacking campaign launched from computers in China. Hackers penetrated the computers of satellite operators, defense contractors and telecommunications c...
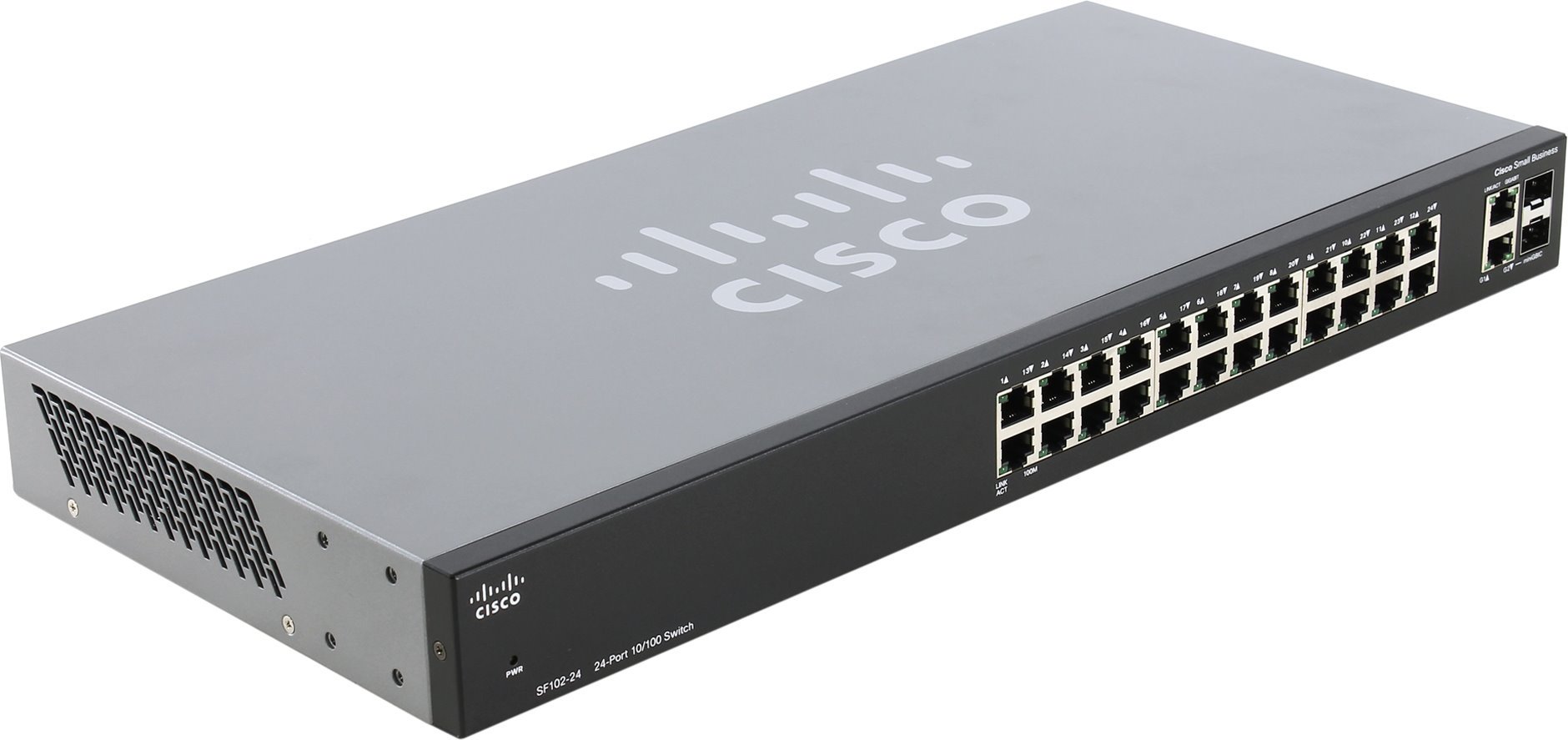
What have you learned about the attack on 200 000 network of Cisco switches?
the Last few days were not the best for cyber security. The Iranian Ministry of communications and information technologies reported that it has also become a victim of global cyber-attacks that (or simply switches) from Cisco, wh...
Russian accused of hacking into LinkedIn, was extradited to the US
the Russian, who is accused of hacking into LinkedIn, Dropbox and Formspring, as well as in compromised personal data of more than 100 million users, has been extradited to the United States after a 15-month detention in Prague, T...
Despite the development of new methods of cyber security, e-wallets and payment systems will always be a tasty morsel for hackers and other dishonest people that live on the world wide web. Have repeatedly made attempts of hacking...
A serious vulnerability in Intel processors can lead to data leakage
Programmers who first discovered the vulnerability, which writes the edition , reporting that it allows any software, including viruses, to access passwords, usernames and other confidential user information. The scale of the prob...
Hackers demand from the creators of "Game of thrones" $ 6 million in bitcoins
a Few days ago, the Internet community stirred up information about what an unknown group managed to steal from the HBO huge amount of confidential information including yet not aired a series of television series "Game of thrones...
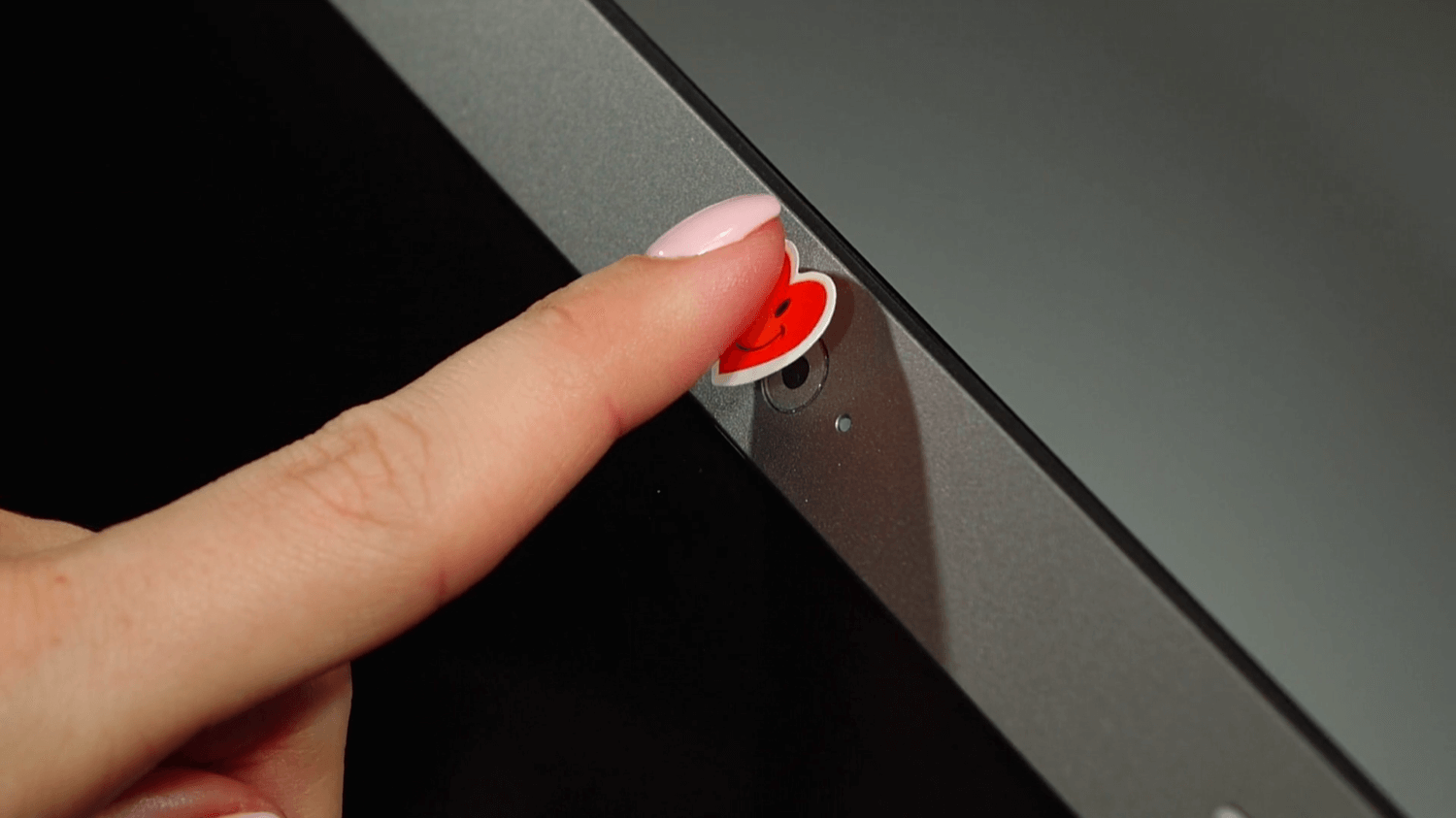
Created the image of the "universal fingerprint" that can fool most sensors
fingerprint Scanners are no longer a novelty on the market of mobile electronics. They are primarily designed to provide additional security for user data, but a 100% guarantee against unauthorized entry, of course, can not give. ...